DOJ Records Show Massive Increase In Warrantless Surveillance Since 2009
Secret surveillance of American citizens has dramatically increased under the Obama Administration.
According to documents obtained today from the Department of Justice by the American Civil Liberties Union, there has been a massive increase in warrantless electronic surveillance since the Obama Administration took office in 2009:
Justice Department documents released today by the ACLU reveal that federal law enforcement agencies are increasingly monitoring Americans’ electronic communications, and doing so without warrants, sufficient oversight, or meaningful accountability.
The documents, handed over by the government only after months of litigation, are the attorney general’s 2010 and 2011 reports on the use of “pen register” and “trap and trace” surveillance powers. The reports show a dramatic increase in the use of these surveillance tools, which are used to gather information about telephone, email, and other Internet communications. The revelations underscore the importance of regulating and overseeing the government’s surveillance power. (Our original Freedom of Information Act request and our legal complaint are online.)
Pen register and trap and trace devices are powerfully invasive surveillance tools that were, twenty years ago, physical devices that attached to telephone lines in order to covertly record the incoming and outgoing numbers dialed. Today, no special equipment is required to record this information, as interception capabilities are built into phone companies’ call-routing hardware.
The numbers speak for themselves:
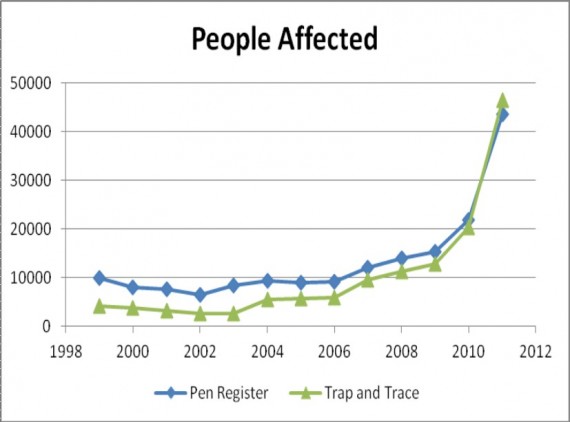
The reports that we received document an enormous increase in the Justice Department’s use of pen register and trap and trace surveillance. As the chart below shows, between 2009 and 2011 the combined number of original orders for pen registers and trap and trace devices used to spy on phones increased by 60%, from 23,535 in 2009 to 37,616 in 2011.
During that same time period, the number of people whose telephones were the subject of pen register and trap and trace surveillance more than tripled. In fact, more people were subjected to pen register and trap and trace surveillance in the past two years than in the entire previous decade
During the past two years, there has also been an increase in the number of pen register and trap and trace orders targeting email and network communications data. While this type of Internet surveillance tool remains relatively rare, its use is increasing exponentially. The number of authorizations the Justice Department received to use these devices on individuals’ email and network data increased 361% between 2009 and 2011
As always, putting this information in a chart makes the dramatic increase in the number of people that have been affected by these surveillance methods exceedingly clear:
For those of you unaware of exactly what kind of information these forms of electronic surveillance can gain access to, the Electronic Frontier Foundation has an excellent summary:
With a pen/trap tap on your phone, the police can intercept:
- The phone numbers you call
- The phone numbers that call you
- The time each call is made
- Whether the call was connected, or went to voicemail
- The length of each call
- Most worrisome, we’ve heard some reports of the government using pen/trap taps to intercept content that should require a wiretap order: specifically, the content of SMS text messages, as well as “post-cut-through dialed digits” (digits you dial after your call is connected, like your banking PIN number, your prescription refill numbers, or your vote for American Idol).
That information is revealing enough on its own. But pen/traps aren’t just for phones anymore — thanks the USA PATRIOT Act, the government can now use pen/trap orders to intercept information about your Internet communications as well. By serving a pen/trap order on your ISP or email provider, the police can get:
- All email header information other than the subject line, including the email addresses of the people to whom you send email, the email addresses of people that send to you, the time each email is sent or received, and the size of each email that is sent or received.
- Your IP (Internet Protocol) address and the IP address of other computers on the Internet that you exchange information with, with timestamp and size information.
- The communications ports and protocols used, which can be used to determine what types of communications you are sending using what types of applications.
- Although we don’t think the statute allows it, the police might also use pen/trap taps to get the URLs (web addresses) of every website you visit, allowing them to track what you are reading when you surf the web. The Department of Justice’s apparent policy on this score is to collect information about what site you are visiting — e.g., “www.eff.org” — using pen/trap taps, but to obtain a wiretap order before collecting information about what particular page or file you are visiting — e.g., “www.eff.org/nsa”. However, there’s no way to confirm that federal authorities actually follow this policy in all cases, and serious doubt as to whether state authorities do.
Pen/tap traps can also be used to determine the location of your cell phone, and presumably you by pinging your phone and using the responses from surrounding cell towers to triangulate your general location. It’s also worth noting, as the report points out, that these figures only cover actions undertaken by the Justice Department. It’s likely that similar techniques are being used by other elements of law enforcement that are not part of the Department of Justice. So, these figures are likely just the tip of the iceberg.
As the ACLU goes on to point out in its post, the legal standard that the government must meet for these forms of surveillance is exceedingly low and doesn’t even require review and approval by a judge. In the case of a wiretap that is actually intended to intercept the content of a phone conversation, law enforcement must submit an application to a judge setting forth sufficient facts to establish probable cause that a crime is being or has been committed and that the wiretap is essential to the investigation of that crime. These types of surveillance, however, are considered “non-content” surveillance, meaning that all law enforcement has to do is file paperwork with a court saying that they stating that they seek information that they believe is relevant to an ongoing investigation. There is no review by a judge, and it isn’t even clear that the paperwork itself is ever actually seen by anyone other than the people in the clerk’s office in which the it is filed. Since the standard for these types of surveillance is so low, the government is able to use them without anyone really asking them to justify at, and certainly nobody questioning their one-sided determination that the information they seek is “relevant” to an investigation.
The problem with this distinction that allows law enforcement to essentially use this method of surveillance with impunity and without review is that it ignores the fact that even this “non content” information can be highly personal and the search invasive:
Non-content information can still be extremely invasive, revealing who you communicate with in real time and painting a vivid picture of the private details of your life. If reviewing your social networking contacts is sufficient todetermine your sexuality, as found in an MIT study a few years ago, think what law enforcement agents could learn about you by having real-time access to whom you email, text, and call. But the low legal standard currently applied to pen register and trap and trace devices allows the government to use these powerful surveillance tools with very little oversight in place to safeguard Americans’ privacy.
It’s also troublesome that the ACLU was required to file a FOIA request, which was fought by the Justice Department, to get this information. This is the kind of information that should be publicly available on a regular basis. There’s little danger that revealing it is going to endanger any ongoing investigations, and the government’s interest in keeping in private is far outweighed by the public’s right to know just how much their government is secretly monitoring American citizens. The ACLU suggests that Congress should tighten the reporting requirements imposed on the Justice Department, but I’m afraid that there would be very little support for such a maneuver on the part of either Republicans or Democrats. One need only look to the overwhelming bipartisan support for the PATRIOT Act to figure that one out. For the time being, it is going to have to take groups like the ACLU educating the public about what is getting done in their name and, hopefully, the American people waking up to what’s happening.
Graphic via CBS News







Very troublesome.
And worse, the only way to undo this is through Congress, and they don’t do much of anything these days.
@mantis:
No, at the federal level, all it takes is Obama telling agencies to stop doing it. Only congress can eliminate the mechanism, but how the mechanism gets used is entirely up to the President.
Obviously, this is all Bush’s fault.
@Stormy Dragon:
No, at the federal level, all it takes is Obama telling agencies to stop doing it.
Like I said, the only way to stop it is through Congress. The executive never declines to use powers it has.
@Jenos Idanian #13:
Well, the PATRIOT Act did make it easier for law enforcement to utilize these forms of surveillance.
@mantis:
And it will always–ALWAYS–push to expand the number and scope of those powers.
It is, as you correctly state, the responsibility of Congress to put the brakes on the executive’s constant attempts to expand its powers. Unfortunately, it’s usually too busy with pointless political exercises and assorted claptrap to actually do its job.
Yeah, this is bad news. Going to have to go after Obama on this one after the election.
Who are the Senators who will best be able to push back on this?
Bully for Team Obama.
Hell, the problem with this program under W. Bush was that we really weren’t using it enough. That needed to change.
We’ve known since Day 1 that we’re in good hands with Panetta, and now Petraeus, and company. They’ve got brass cojones. And they don’t give a rat’s ass about the loopy left. Neither does Obama. That’s a good thing.
@Tsar Nicholas:
Yea who cares about silly thinks like civil liberties and individual rights? We can trust Big Brother!
In other news, the sun rises in the east and sets in the west.
Just out of curiosity, who…. here…. is a card carrying member of the ACLU?????
Why do I have the feeling that I am the only person here who can answer that question in the affirmative?
@OzarkHillbilly:
I am not a member but I do appreciate their work.
@OzarkHillbilly: And for the record, got my renewal notice today. (unsure how many years…. between 6 & 8 I think, tho it could be 10 or 5)(seriously, I do not keep track of this stuff).
@Doug Mataconis:Doug, I think most people, in the abstract, appreciate their work. I can only say, membership is cheap, and it gives one a whole lot of pass on civil liberties issues!!!! snark.
Seriously, they defend every bodies rights (even the KKK’s free speech)… and for $50(or more if one chooses) you can help them.
Sadly, these past couple years, I have been able to give them only the bare minimum. Some day, I hope to make it to the convention.
The rule of thumb here is that any executive power than can be exercised will be exercised.
@OzarkHillbilly:
Just out of curiosity, who…. here…. is a card carrying member of the ACLU?
I am. I send them money every year. You know who doesn’t get my money? Politicians.
@Dave Schuler: Exactly.
@mantis:
Good.
Well, I have given money to Obama, Robin Carnahan, and McCaskill. A rogues gallery if ever there was one…. But consider the alternative? Blunt, Akin, and McCain/Romney…. What choice did I have?
And this is why, even if the guy in office is “your” guy and you trust him completely, you should always oppose any expansion of government power, especially unchecked executive power. It will always expand. Eventually, it will always be abused.
@mantis: And just out of curiosity… Who here remembers when being a “card carrying member of the ACLU” was the worst insult possible? You know…. Freedom of the press? Pttthhhhh…. Freedom of speech and Assembly???? HA! Religion??? FU, you can take my religion and love it too!
I really did not understand those years. When people say these years are fu’d up, I remember times that are not so different.
@mantis:
“doesn’t” isn’t the same as “can’t”. Presidents are still responsible for their decisions.
@Stormy Dragon:
I live in the real world. You should visit sometime.
Besides, even if we found a president to take a principled stand, it’s a temporary job.
@mantis:
tl;dr: It’s okay when a Democrat does it.
@Stormy Dragon:
It’s okay when a Democrat does it.
It’s not, actually.
@Stormy Dragon: I like how all libertarian thinking can be reduced to “both sides do it” when you press them long enough.
Who cares? In the one party state, there is no reason for anyone to complain about such issues. This shows that politics in the future will not be about torture, evolution, stem cells, drones, or surveillance. Those who currently follow politics have to just realize that the future is about entitlements, who gets them, and who pays for them. There is no status in worrying about issues that we just used to bash Republicans when the Republicans are irrelevant.
@Tillman:
No one should comment on the Emperor’s clothes? Ok, understood.
though, politically trying to think of the up side for Obama (or Romney) to stop the wiretaps, drone attacks, raids on state legal pot operations. On these issues, either would be hit with the terrorist and criminal coddler labels and get distracted from the “vote for Oceania, vote for me” message. Either could have ridden out the exercise of discretion on deportations Obama did because hey, cheap non union labor.
@OzarkHillbilly: Yes, but you have an ability to recall events that happened less than a nanosecond ago.
@Just ‘nutha ig’rant cracker: That should have been “more”, sorry.
@OzarkHillbilly:
Nope. I am.
Obama is a civil liberties disaster. It would be nice if that fact got more coverage and less excuse making from his supporters.
Obama ‘Even Worse’ Than Bush On Secret Wiretapping Case, Says S.F. Lawyer
DOJ during the Bush administration imprisoned me without a criminal charge in order to screw up my third party civil lawsuit. I think my judge Edward Nottingham was bribed.
http://www.ca10.uscourts.gov/downloadmisconduct.php?fileid=62
I think that DOJ went along with this because Nottingham’s USMS guards were also involved with prostitutes and strippers and because they didn’t want to reopen criminal convictions of Joe Nacchio etc. http://www.denverpost.com/commented/ci_6598184
I thought everything would be different when Obama was elected. Instead DOJ claimed in Court that the Prisoner Tracking System and the Joint Automated Booking System can be used without a criminal charge. Not according to DOJ’s Notices in the Federal Register see Vol 66 p. 20478 Vol 69 p. 23213. In order to get my claims dismissed, DOJ actually misrepresented their own notices in the Federal Register. The judge didn’t verify the Federal Register Notices himself, he just believed DOJ.
Now DOJ can take photos of anyone’s body and their fingerprints and put them on a national database. https://ecf.dcd.uscourts.gov/cgi-bin/show_public_doc?2011cv1032-36
In my case, DOJ made up non-existent criminal charges and entered them into the NCIC and the Warrant Information Network but the people responsible went unsanctioned:
http://usmsinternalinvestigation.blogspot.com/
http://www.lawlessamerica.com/index.php?option=com_mtree&task=viewlink&link_id=1996&Itemid=100