Microsoft Finds New Windows Security Flaws
WaPo: Microsoft Finds New Windows Security Flaws
Microsoft Corp. said yesterday that it had identified a host of new security flaws in its software, some of which could allow hackers to remotely commandeer vulnerable computers, and it urged users to install a series of software updates to address the problem.
Computer experts said it appeared that hackers had not yet exploited any of the security holes. The vulnerabilities were discovered mostly by computer security firms and researchers, who alerted Microsoft so it could develop solutions. The company posted four security bulletins on its Web site yesterday as part of a monthly effort to release updates to its Windows operating system software.
The Web site (www.microsoft.com/security/) leads users through the steps they need to follow to download and install the updates. Patches are available for Windows NT 4.0, Windows 98 and newer releases, including Windows Me and XP.
Microsoft rated three of the four security bulletins as critical, requiring prompt attention. The fourth it rated important. It said the critical bulletins accounted for 20 vulnerabilities in various versions of the company’s Windows software.
“Number-wise, it is an amount that is unusual,” said Stephen Toulouse, security program manager with Microsoft’s Security Response Center, though he was not sure whether it was the largest number of security holes the company has addressed at one time.
I understand that Windows is an incredibly complex piece of software and that the flexibility that made it the dominant operating system also makes it vulnerable. But one would think that, once a piece of software has been on the market for several years, the kinks would have been ironed out.

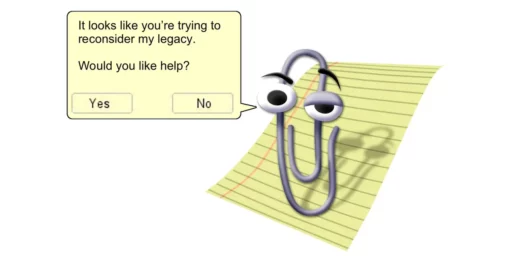


Don’t forget that the reason there were a “host” of vulnerabilities (four is a “host?”) addressed yesterday is because Microsoft recently changed how they handle security updates, as mentioned in the Post article. Instead of issuing them as they occur, they’re grouping them together for the release on the second Tuesday of every month.
If they feel a vulnerability is too severe to wait that long, they’ll issue that fix immediately.
Yep. Only took 2 hours to download 3MB of fixes… People must have really hammered the update web site.
But one would think that, once a piece of software has been on the market for several years, the kinks would have been ironed out.
Logically, it would seem that since updates designed to fix vulnerabilities are often rolled out more hastily than the original operating system, the problem may be that a lot of the recent vulnerabilities were opened by past updates.
Fixing security flaws isn’t their priority. XP is the 3rd complete rewrite I think and it seems to have MORE flaws than older versions.
One of the main problems is that Windows was originally a single user system and each new version is designed to be 100% compatible with software that runs on older versions. Apple bit the bullet to go from OS9 to OSX. Bill isn’t interested in doing that because when you have a monopoly there’s really no benefit to improving quality.
The lack of stability and security is probably a major reason why about 40% of their customers are looking for a way to exit the Microsoft software ecology. Eventually they will find a way.
yeah, the bimonthly security upgrade.
That is why I run my own site on a set of clustered linux and solaris machines.
—