Lieberman’s Campaign Manager On Website Problems (Video)
Sen. Lieberman’s campaign manager Sean Smith was just on FOX News to talk about the website troubles that have plagued the Lieberman campaign since yesterday morning and, according to Smith, the Lieberman campaign is taking this very seriously: the campaign has asked for an investigation by the Connecticut Attorney General and the United States Attorney’s Office. Smith also likens this to the Republican phone jamming scandal in New Hampshire in 2002 in which “jail terms were handed down.”
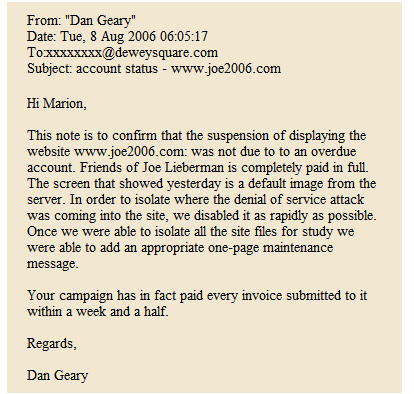
So, to state the obvious, all that seems like one hell of a bluff by the Lieberman camp if they simply forgot to pay their bills as alleged by the Lamont campaign. And that’s not to mention the following letter from Lieberman’s internet consultant Dan Geary (via TPMmuckraker) alleging foul play as well:
When I first posted about this last night, the details were incredibly sketchy and I didn’t want to point fingers. But at this point, it seems very likely that this was the deliberate work of someone determined to derail the Lieberman campaign on the eve of the Democratic primary.
UPDATE: More via Paul Keil at TPMmuckraker:
I just got off the phone with the internet consultant to Joe Lieberman’s campaign, Dan Geary. And he says that the site has been “fatally compromised” by an unknown hacker. In addition, all email addresses with the Joe2006.com domain are down too; the attack, Geary says, has “disrupted the entire campaign.”
Geary, who developed and oversees Lieberman’s site, Joe2006.com (and says that the campaign has paid their account in full), said that an attack starting mid-morning yesterday had “red-lined” the server. “We can’t even get the site up,” he said. “We even tried putting up a single, blank page. It red-lined the entire network. This guy’s got our number.”
Geary said that they believed it to be a “denial of service” attack, meaning there are so many queries to the network that it becomes unstable. He did not have any information as to the source of the attack or any idea about the identity of the hacker. “We’re just fighting to get something live,” he said, “we’re not security experts.” He also said that it would be up to the campaign as to whether they would refer the case to the FBI.
This was not the first time that the site was attacked. Earlier, a hacker “got through one of the functions on the site,” Geary said. The hacker then did a “SQL injection,” ultimately replacing the index page. The front page of the site then read “We ownz you site.” It was signed “thhacker.”
But yesterday’s and today’s was a different kind of attack. Whoever the hacker is “saved the best until the last day,” Geary said.
UPDATE (James Joyner): I should note that a redirect to an “Account suspended – Please contact site host” page is apparently fairly typical. OTB went down toward the end of my dealings with HostingMatters and visitors got a nearly identical message for several hours that day. The problem was that the site was executing too many processes and overwhelming my shared hosting account, not a lack of payment on my part. Apparently, it’s the default error message they use.
UPDATE: There’s AP coverage here, Allah Pundit will be covering all the developments in Freshmaker vs. Joementum here, and Michelle Malkin has some good links here.
UPDATE (James Joyner): Commenter Len points to Kos‘ post saying that Lieberman’s site was “paying $15/month for hosting at a place called MyHostCamp, with a bandwidth limit of 10GB. MyHostCamp is currently down, along with all their clients.” I don’t know what his source is for this information but it strikes me as quite plausible, as that was essentially the problem OTB was having with HostingMatters.
Most blogs and campaign sites can get by with that kind of hosting about 360 days of the year with no problems whatsoever but, if you simply have to be up, then you have to go with a dedicated server. OTB did that quite some time ago and, if present trends continue, will likely have to upgrade to a substantially more expensive one before long. Kos say he spends over $7000 a month on hosting, which is simply mindboggling.





Why would someone want to “derail” Liebermans’ campaign? Its not like it has been any kind of steamroller.
This just Lieberman’s way of saving face. he’s ging to play to the stereotype of all those cumputer nerks for Lamont who supposedly know how to do amazing things to computers to pretend that the race was unfair. It’s childish.
There isn’t anything on Joe’s site to help voeters. The net effect (in terms of Joe’s voters turning out) of his site being down is zero. This is strictly theater.
I should have spellchecked that!
all that seems like one hell of a bluff by the Lieberman camp
If it wins him the primary, what do they care?
Another conspiracy?
I’m telling ya… everything’s a conspiracy these days!
I just do not understand why y’all have so much difficulty believing that the Bush administration blew up the World Trade Center. You sure have no problem believing everything else thrown your way.
Kos has what really happened to Joe’s site, by the way… just in case you’re interested. (I am fully aware that you are not inclined to believe anything that Kos has to say, but I think he has the goods on this one.)
Denial of service attacks are a dime a dozen. Any experienced net manager knows how to handle them. There are numerous techniques for handling them starting with IP blocking. Geary makes it sound like some sort of novel, highly dangerous threat, but the fact is that a good web site provider has several techniques to protect against them.
Also, a supposed Internet manager saying this :
“He did not have any information as to the source of the attack or any idea about the identity of the hacker. “We’re just fighting to get something live,†he said, “we’re not security experts.—
Anyone who claims to be an interenet consultant and says this should be fired on the spot. And getting the source of the attack is truly trivial for most DoS attacks. Unless there are a huge DDos attack, but if so we would have seen plenty of other Internet signs.
Finally, anyone who knows something about Denial of Service attacks (which essentially just means fake requests for a web page that overwhelm the servers) will find the idea that the the ‘site has been “fatally compromised†by an unknown hacker.’ risible.
My guess ? There probably was a DoS attack. However, the web hosting service has to be totally incompetent to not block it. Instead, it probably crashed their servers. Again, either they were totally incompetent, so they had no backup or couldn’t get anything up. They may be trying to blow up a relatively minor attack to cover their incompetence.
Lieberman’s server MyHostCamp is down. It’s a cheapo 15 dollar a month outfit with 75 other sites to serve. Hacking had nothing to do with it.
I’m not expecting the Lieberman camp to apologize although they have offically admitted that they have no evidence of a Lamont hacker. That’s about as much integrity as one can reasonably expect from them, I guess..
Erg is right.
This is just another of many examples of 25 year-olds who think HTML and JAVA are programming languages.
Anything tougher than that passes their knowledge level.
BUT, they’re cooool…..
Here’s another one for you – that note that “confirms” the site outage wasn’t due to unpaid accounts? That note is from Dan Geary, the guy who runs the website and works for Lieberman’s campaign. He is simply not the concrete authority on whether or not the hosting company shut them down for non-payment. That would be the hosting company.
Surely some enterprising young soul could contact them directly and ask this question… unless it’s actually easier to just go on Faux news and cry DoS!
Sometimes seems like everyone on the net is an IT expert. Well, I am not. So could any of the experts answer a very basic question – one that I always wondered about?
Why would a huge spike in requests to a server cause the server to crash? Where I am going with this is – why do servers not have some function which would allow them to simply turn away requests that are in excess of their capacity to handle, thus staying online and handling what they can? Why does the whole thing come crashing down?
Why would a huge spike in requests to a server cause the server to crash? Where I am going with this is – why do servers not have some function which would allow them to simply turn away requests that are in excess of their capacity to handle, thus staying online and handling what they can?
The simple answer is that a web hosting site is not one system, but a whole complex of systems network switches, network cards, web servers, database servers, name servers, disk arrays etc. all of which have different choke points. And you cannot just throw traffic away, because most clients will retransmit, which actually INCREASES the load. The traffic needs to be throttled down, which is not easy at all the levels and systems. Even to get to the point where you want to print a simple page saying “Site too busy” could lead to enough load on other systems (network cards and buffers) that it could strain your server.
Now its possible to design around all of these issues, and huge sites like Google and much smaller sites do just that, but it takes money, hardware and the like. A very small webhosting service just will not (or cannot) do that sort of design for you.
re: Kos’s site is run by a number of full time paid admins. Not just one. But I think the group also helps run other related sites.
MyDD has crashed. For a joke they’re starting a rumor that the Liebliars have hacked them.
I don’t know which is worse, the lies from the Lieberman campaign or the incompetent, dishonest reporters who lap it up.
For what it’s worth, the New Haven Independent is reporting,
Sounds plausible to me.
The fact that a US Senator running a campaign did not have his own box with a competent admin, or at least a third-party hosting service with the level of resources and competence required for the campaign is just more proof Lieberman is an idiot, not that more was necessary.
Greywolf:
Sorry, but Java IS a programming language. But, you’re cooool….
Tano:
This is exactly what a Denial of Service (DoS) attack does. The attacking connections use up all available resources, and any legitimate traffic gets turned away. Their “Service” is “Denied”. Now DoS attacks come in 3 flavors:
1.) A standard DoS attack, and the original incarnation, is one host against another, sending out as many packets as possible. Whoever has the most bandwidth wins.
2.) A Distributed DoS (DDoS) uses multiple attacking computer against a single host. The attacking computers can range into the thousands, and usually belong to innocent people who have had their computer hijacked by a trojan or virus.
3.) The latest and hardest to stop is a Reverse DDoS. In this form, a single attacking computer will send a flood of bad packets to multiple innocent hosts, while faking (spoofing) the attacker’s source IP address. Then the innocent hosts will reject the packet, and send the rejection back to the fake IP address, causing a DDoS against that IP.