The Mumbai Terrorist Attacks and “Open Source” Warfare
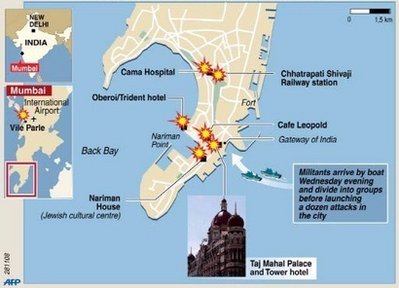
We still don’t know for certain yet why the attacks in Mumbai took place or who the perpetrators were and we may not know for quite a while if ever. There are lots of speculations and accusations but precious little hard data. We don’t even know for certain how many were in the group that attacked Mumbai last week. The Indian government says ten, presumably because nine were killed and one captured. Among the things we do know are that
- They were Muslims or wanted us to believe they were Muslims. There are enough first-hand reports of the attackers screaming “Allaho akbar” that it’s a reasonable conclusion. Whether they were Islamist radicals, Indian or Pakistani, members of this group or that is getting ahead of the data.
- They used the techniques of what John Robb has called “open source warfare”:
THEIR battle fatigues are jeans, T-shirts and trainers. They are the new breed of terrorist — using everyday technology as a weapon of war.
Among their arsenal of weapons are bags of almonds and BlackBerry mobile phones — almonds to keep their energy up, and the mobile internet connections to stay one step ahead of police and the military.
They are the new breed of terrorist — using everyday technology as a weapon of war.
[…]
One of the rucksacks carried by one of the terrorists, later recovered by commandos, contained a Mauritian national’s identity card, Chinese-made grenades, seven ammunition magazines, 400 spare rounds of ammunition, seven credit cards from different banks, dry rations and thousands of dollars in cash.
However amid the arsenal of military hardware, it was the use of humble mobile phones and internet technology that proved a key weapon — one which caught the anti-terrorist forces by surprise.
The use of BlackBerrys by the terrorists to monitor international reaction to the atrocities, and to check on the police response via the internet, provided further evidence of the highly organised and sophisticated nature of the attacks.
The gunmen were able to trawl the internet for information after cable television feeds to the two luxury hotels and office block were cut by the authorities.
The physical evidence and first-hand reports are enough to draw this conclusion.
A post at Defense and the National Interest takes note of this and warns:
The urgency of the cyber threat and the extent to which readily available technology is being used against us to heinous effect presents serious challenges to the nation and to our community. Not to mention, the difficulties we face in countering these tactics by providing useful information quickly and down to the lowest levels of the chain of command.
In his column this morning David Ignatius warns of the possibility of a Mumbai-like attack being mounted on one of our cities:
What would happen if roving gunmen infiltrated U.S. cities and started shooting? Most U.S. police departments aren’t well prepared to deal with such “active shooters,” as they’re called. Police are trained to cordon off an area that’s under attack and then call in a paramilitary SWAT team to root out the gunmen. But what if the attackers keep moving and shooting? The response can be haphazard, as was clear in such disparate incidents as the 2002 Beltway sniper attacks in the Washington area and last year’s massacre at Virginia Tech.
“Mumbai is a worst-case ‘active shooter’ problem,” says a former CIA officer who helped organize a DHS pilot program on the subject last summer for police chiefs. “It had multiple shooters, multiple locations, mobile threats, willingness to fight the first responders and follow-on SWAT/commando units, well-equipped and well-trained operatives, and a willingness to die. Police department commanders in America should be scratching their heads and praying.”
What, if anything, should we be doing to foreclose such attacks? Are we doing enough? Too little? Too much?
I’d appreciate your thoughts and suggestions in the comments. I’ve put a few more thoughts of my own over at The Glittering Eye.




Heh. CNN was a help, there, as well.
The reports we got from the planes involved in the 9/11 atatcks suggested that the onboard TV systems were being used to monitor reaction, too, particularly to my memory in the case of the plane that went down in PA, after the victims revolted.
But you now, as to the blackberry thing, it strikes me as reasonable to jam mobile phone signals in the area involved in such an attack as a first response. THere’s some chatter in the last few weeks from Canada about such boxes.
It’s true enough that such deployment causes problems for the good guys, too, but I would guess those to be more than offset by the crippling of the bad guys comms.
Not to get off track….but is it plausible that the intent was similar to the bombing of the Golden Mosque in Iraq?. Stir the pot between rivals…in this case, push India and Pakistan to heightened defensive alertness or possibly a skirmish thus Pakistan would be using forces in places other than Waziristan?…it’d even let Pakistan off the hook for the little terrorist hunting they do.
Surely if they just wanted to kill Jews/Americans/Euros there are other soft targets to hit with greater potential death tolls…more bang for the buck if you will.
If you want the opinion of a well-regarded security consultant, check out Bruce Schneier’s blog:
http://www.schneier.com/blog/
Basically he says that shutting down communications is a bad idea, and there’s basically no countermeasures you can take to stop this stuff, so keep in mind that this kind of thing is extremely rare, don’t overreact, and try to have the best intel you can.
Schneier tries to stay pretty apolitical, but having read his blog for several years, what he means by the last sentence, IMO, is: Bin Laden got what he wanted when Bush attacked the middle east, and these terrorists will get what they want if India and Pakistan go to war. Hope that doesn’t happen.
Charles, here’s the rub on an event being extremely rare: every time it recurs it becomes less rare. While I don’t discount it completely I think we should be cautious about using the persistence theory in our planning.
Not to be snide but, start digging more graves?
Seriously, I see very little that could possibly be done to foil such an attack. Any police force in most any major city could easily be quickly overwhelmed by such an attack. They just are not set up to deal with such things, and the cost of getting them set up would be prohibitive, starting with a whole lot more cops on the street, and all of them going thru SWAT training, as well as equipping them the same, etc.
This struck me as obvious when bit first said it, but after thinking about it, I am not so sure. All cell phones have GPS transmitters, maybe that could be used against them? (I am mindful of the techno/civil liberty problems, but maybe?) Besides, FRC radios are cheap, easy to use, have decent range, good battery life, and a simple code could be made up to talk in.
On the other side of the communications coin tho, make police scanners illegal? (I know, that opens up a whole ‘nother can of worms…)
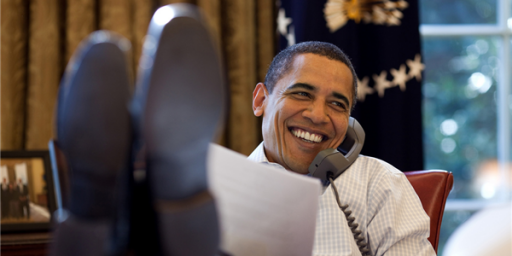
Wait a second, don’t these terrorists know that we just elected Barack Obama as our president? Or is it that the world continues to be a dangerous place and it also continues to be much easier to destroy than to build. I can’t imagine wanting to live in a country that could somehow stop or respond to these kind of events as instantaneously as some seem to desire.
1. Don’t over-react;
2. Don’t jump to conclusions about what’s going on: wait for a reasonable assessment;
3. Be thankful that some exercise their 2nd Amendment rights;
4. Hope you or a loved one is not there.